Today I will talk about how to localize a virus if it did penetrate your computer, how to defeat Trojans and how to restore the system after a rootkit infection if everything has gone too far.
So, if you suspect that your computer is infected, the first thing you should do is:
- disconnect the computer from the Internet (pull out the UTP cable, turn off Wi-Fi);
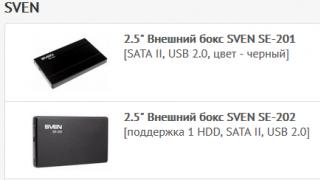
- disconnect all external devices from the computer (external hard drives, flash drives, phones, etc.).
All this must be done to isolate the infected computer from the outside world. It is imperative to disconnect the computer from access to the outside world via the Internet and from the local internal network, since the malware will almost certainly try to spread itself to the entire segment accessible to it.
In addition, if the malware is part of a botnet network or contains components, then it will be inactive and activated at the moment when a control command is received from the external network. This will also insure us against leakage of local data into the network, for example, through DNS tunneling or similar hacker things.
Registry recovery
The Windows registry, starting from the very first versions of the OS, remains a critical component of the system, in fact, it is a database for storing various parameters and settings of the working environment, installed software and Windows itself. It is logical that a violation of the registry or its damage threatens the inoperable state of the OS.
The registry itself, which is opened by the standard regedit utility, is physically represented by several files stored along the path %SystemRoot%\System32\config\. These are files named SYSTEM, SOFTWARE, SECURITY, SAM, DEFAULT without extensions and available only to NT AUTHORITY\SYSTEM, LocalSystem system processes. But if the registry is opened through a regular editor, then these files will appear as a large hierarchical tree.
The first thing that comes to mind is, of course, to make backups of these files and, if necessary, simply replace the broken ones with backups. But from under the loaded OS, it will not be possible to do this by simple copying, and exporting data using regedit may turn out to be defective. Therefore, consider the tools that will help us in this matter.
Regular Windows tools to restore the registry
Out of the box, Windows, unfortunately, does not have a separate tool that allows you to backup the registry. All that the system can give is the functionality of the obsolete NTBackUp, originally from the era of Windows XP / 2003 Server or in the new Windows 7, 8, 10 operating systems, its reincarnation in the form of "", offering to create an entire system image (of the entire system - not the registry! ). Therefore, we will consider only a small example of actions in the recovery console that allow you to restore the registry manually. In fact, these are operations to replace broken files on an infected system with original registry files from a backup made in advance.
NTBackUp utility interface
After booting in Live CD mode from the installation disk or from a locally installed recovery console (for XP/2003), you need to run the following commands, described by Microsoft itself:
// Back up the system registry
md tmp
copy c:\windows\system32\config\system c:\windows\tmp\system.bak
copy c:\windows\system32\config\software c:\windows\tmp\software.bak
copy c:\windows\system32\config\sam c:\windows\tmp\sam.bak
copy c:\windows\system32\config\security c:\windows\tmp\security.bak
copy c:\windows\system32\config\default c:\windows\tmp\default.bak
// Delete broken files from the OS system directory
delete c:\windows\system32\config\system
delete c:\windows\system32\config\software
delete c:\windows\system32\config\sam
delete c:\windows\system32\config\security
delete c:\windows\system32\config\default
// Copy healthy registry files from the shadow copy
copy c:\windows\repair\system c:\windows\system32\config\system
copy c:\windows\repair\software c:\windows\system32\config\software
copy c:\windows\repair\sam c:\windows\system32\config\sam
copy c:\windows\repair\security c:\windows\system32\config\security
copy c:\windows\repair\default c:\windows\system32\config\default
Everything, reboot the machine and look at the result!
Advanced Registry Repair Methods
As we found out, Windows does not have a decent registry management tool. Therefore, let's see what third-party manufacturers can offer us.
TCPView utility windowThe list of network services and the reserved ports for NT systems corresponding to them can be found in the %SystemRoot%\system32\drivers\etc\services file - this is also essentially a text file without extension, which can be viewed with any notepad.
Nirsoft CurrPorts utility windowAnd finally, for everything described above that we did with our hands, you can use tools, for example. This utility restores system network settings registry keys to default values. In addition, she also:
- checks the hosts file for the correctness of the localhost pointer (must refer to the address 127.0.0.1);
- creates a backup of the current system settings (at the request of the user);
- disables all network adapters and reinstalls their settings.
 WinSock XP Fix utility window
WinSock XP Fix utility window The native GUI tool we talked about does the same thing as the netsh int ip reset and netsh winsock reset commands. The Reset-TCPIP tool is similar to it, which performs all the described combinations of console commands under one GUI.
Reset-TCPIP utility windowAnother good free tool is designed to fix a variety of errors related to the network and the Internet in Windows. A short list of its features:
- clear and fix the hosts file;
- enable Ethernet and wireless network adapters;
- reset Winsock and TCP/IP protocol;
- clear DNS cache, routing tables, clear static IP connections;
- reload NetBIOS.
Live CD as a lifeline
And, continuing our topic, we just could not get past the story about Live CD assemblies intended for system recovery. Initially, Live CD was positioned as a tool for performing administrative tasks: preparing a hard drive, quickly gaining access to data stored on disks, and so on. Now Live CDs are more like a universal lifeline for resuscitation of the system in case of various crashes, including after a virus attack. Their main advantage is that all tools are assembled under one hood and can work in parallel. But there is also a drawback: in order to boot into Live CD mode, you need to reboot the machine, which in some cases is unacceptable for us.
All well-known anti-virus developers have free boot disks for system recovery. We will briefly go over them, but we will not go into details - we agreed at the beginning of our material that we will use only those tools that are not pure anti-virus software.
My best friend brought me a netbook that was heavily infected with viruses and asked me to help clean the system from the zoo. For the first time I saw with my own eyes a funny branch in the development of malware: “ransomware”. Such programs block some functions of the operating system and require you to send an SMS message to receive an unlock code. The treatment turned out to be not entirely trivial, and I thought that perhaps this story would save someone some nerve cells. I tried to provide links to all sites and utilities that were needed during the treatment.
In this case, the virus pretended to be the Internet Security anti-virus program and required SMS K207815200 to be sent to 4460. There is a page on the Kaspersky Lab website that allows you to generate ransomware response codes: support.kaspersky.ru/viruses/deblocker
However, after the introduction of the code, the OS functions remained blocked, and the launch of any anti-virus program led to the instant opening of a virus window that diligently emulated the operation of the anti-virus:
Attempts to boot into safe modes led to exactly the same result. Also, the matter was complicated by the fact that the passwords for all administrator accounts were empty, and logging in to a computer over the network for administrators with an empty password was closed by default by policy.
I had to boot from a USB Flash disk (by definition, a netbook does not have a disk drive). The easiest way to make a bootable USB drive is:
1. Format the disk in NTFS
2. Make the partition active (diskpart -> select disk x -> select partition x -> active)
3. Use the \boot\bootsect.exe utility from the Vista/Windows 2008/Windows 7 distribution: bootsect /nt60 X: /mbr
4. Copy all distribution files (I had a Windows 2008 distribution at hand) to a usb disk. Everything can be loaded.
Since we don’t need to install the OS, but treat viruses, we copy a set of free cures (AVZ, CureIt) and auxiliary utilities (looking ahead, I needed Streams from Mark Russinovich) and Far to disk. We reboot the netbook, set the BIOS to boot from USB.
The Windows 2008 installer is loaded, we agree with the choice of language, Install now and then press Shift + F10. A command prompt window appears from which we can run our antivirus tools and look for an infection on the system drive. Here I ran into a difficulty, CureIt dropped the system into the blue screen of death with swearing at the error of working with NTFS, and AVZ, although it worked out, could not find anything. Apparently the virus is very, very fresh. The only clue is a message from AVZ that it found executable code in an additional NTSF stream for one of the files in the Windows directory. This seemed strange and suspicious to me, since additional NTFS streams are used in very specific cases and nothing executable should be stored there on normal machines.
So I had to download the Streams utility (http://technet.microsoft.com/en-us/sysinternals/bb897440.aspx) from Mark and delete this stream. Its size was 126464 bytes, just like the dll files that the virus laid out on flash drives inserted into the system.
After that, I used Far to search the entire system disk for files of the same size and found 5 or 6 more suspicious files created in the last 2-3 days. They were removed the same way. After that, CureIt was able to work (apparently it stumbled on additional threads) and successfully cleaned out two more trojans :)
After the reboot, everything worked, additional runs of anti-virus scanners did not find anything. With the help of AVZ, policies were restored that limited the functions of the OS. A strict suggestion was made to a friend about how important it is to use antiviruses, especially since there are many free ones (
Like
Like
tweet
There are universal programs like a Swiss knife. The hero of my article is just such a "universal". His name is AVZ(Antivirus Zaitsev). With the help of this free You can catch antivirus and viruses, and optimize the system, and fix problems.
AVZ features
I already talked about the fact that this is an antivirus program in. About the work of AVZ as a one-time antivirus (more precisely, an anti-rootkit) is well described in its help, but I will show you the other side of the program: checking and restoring settings.
What can be "fixed" with AVZ:
- Repair startup programs (.exe, .com, .pif files)
- Reset Internet Explorer settings to default
- Restore Desktop Settings
- Remove rights restrictions (for example, if a virus blocked the launch of programs)
- Remove banner or window that appears before login
- Remove viruses that can run with any program
- Unblock Task Manager and Registry Editor (if the virus has prevented them from running)
- Clear File
- Disable autorun programs from flash drives and disks
- Delete junk files from hard drive
- Fix desktop issues
- And much more
It can also be used to check the safety of Windows settings (in order to better protect against viruses), as well as optimize the system by cleaning startup.
The AVZ download page is at .
The program is free.
First, let's protect our Windows from careless actions
The AVZ program has very many functions affecting the operation of Windows. it dangerous, because in case of an error, trouble can happen. Please read the text and help carefully before doing anything. The author of the article is not responsible for your actions.
In order to be able to "return everything as it was" after careless work with AVZ, I wrote this chapter.
This is a mandatory step, in fact, the creation of a "retreat" in case of careless actions - thanks to the restore point, it will be possible to restore the settings, the Windows registry to an earlier state.
Windows Recovery is a required component of all versions of Windows, starting with Windows ME. It is a pity that they usually do not remember about it and waste time reinstalling Windows and programs, although it was possible to just click a couple of times with the mouse and avoid all problems.
If the damage is serious (for example, some system files have been deleted), then System Restore will not help. In other cases - if you configured Windows incorrectly, "tricked" with the registry, installed a program from which Windows does not boot, incorrectly used the AVZ program - "System Restore" should help.
After work, AVZ creates subfolders with backups in its folder:
/backup- backup copies of the registry are stored there.
/Infected- copies of removed viruses.
/quarantine- copies of suspicious files.
If problems started after AVZ was running (for example, you thoughtlessly used the AVZ System Restore tool and the Internet stopped working) and Windows System Restore did not roll back the changes made, you can open registry backups from the folder backup.
How to create a restore point
Let's go to Start - Control Panel - System - System Protection:
Click "System Protection" in the "System" window.

Click the "Create" button.

The process of creating a restore point can take up to ten minutes. Then a window will appear:

The restore point will be created. By the way, they are automatically created when you install programs and drivers, but not always. Therefore, before dangerous actions (configuring, cleaning the system), it is better to once again create a restore point, so that in case of trouble, praise yourself for your forethought.
How to restore your computer using a restore point
There are two options for launching System Restore - from under running Windows and using the installation disc.
Option 1 - if Windows starts
Let's go to Start - All Programs - Accessories - System Tools - System Restore:

will start Choose a different restore point and press Further. A list of restore points will open. Choose the one you need:


The computer will automatically restart. After downloading, all settings, its registry and some important files will be restored.
Option 2 - If Windows won't boot
You need an "installation" disk with Windows 7 or Windows 8. Where to get it (or download), I wrote in.
We boot from the disk (how to boot from boot disks, it is written) and select:

Choose "System Restore" instead of installing Windows


Repairing the system after viruses or inept actions with the computer
Before all actions, get rid of viruses, for example, using. Otherwise, there will be no sense - the corrected settings will be "broken" by the running virus again.
Restarting Programs
If a virus has blocked the launch of any programs, then AVZ will help you. Of course, you also need to start AVZ itself, but it's pretty easy:
First we go to Control Panel- set any type of view, except for Category - Folders settings - View- uncheck Hide extensions for registered file types - OK. Now each file has extension- a few characters after the last dot in the name. Programs usually .exe and .com. To run AVZ antivirus on a computer where programs are prohibited, rename the extension to cmd or pif:

Then AVZ will start. Then in the program window itself, press File - :

Points to be noted:
1. Restore launch options.exe, .com, .pif files(actually solves the problem of running programs)
6. Remove all Policies (restrictions) of the current user(in some rare cases, this item also helps to solve the problem of starting programs if the virus is very harmful)
9. Removing system process debuggers(it is highly desirable to note this item, because even if you checked the system with an antivirus, something could remain from the virus. It also helps if the Desktop does not appear when the system starts)
, confirm the action, a window appears with the text "System Restore Completed". After that, it remains to restart the computer - the problem with starting programs will be solved!Desktop startup recovery
A fairly common problem is that the desktop does not appear when the system starts.
Run Desktop you can do this: press Ctrl + Alt + Del, launch the Task Manager, there we press File - New Task (Run...) - enter explorer.exe:

In order not to do this every time, you need to restore the program launch key explorer("Explorer", which is responsible for the standard viewing of the contents of folders and the work of the Desktop). In AVZ we press File- and mark the item

Unlock Task Manager and Registry Editor
If the virus has blocked the launch of the two above-mentioned programs, the ban can be removed through the AVZ program window. Just check two things:
11. Unlock Task Manager
17. Unlock Registry Editor
And press Perform the marked operations.
Problems with the Internet (Vkontakte, Odnoklassniki and antivirus sites do not open)
Cleaning the system from unnecessary files
Programs AVZ can clean the computer from unnecessary files. If the hard disk cleanup program is not installed on the computer, then AVZ will do, since there are many possibilities:

More about points:
- Clear system cache Prefetch- cleaning the folder with information about which files to load in advance for quick launch of programs. The option is useless, because Windows itself quite successfully monitors the Prefetch folder and cleans it up when required.
- Delete Windows log files- you can clean up a variety of databases and files that store various records of events occurring in the operating system. The option is useful if you need to free up a dozen or two megabytes of hard disk space. That is, the benefit from using is scanty, the option is useless.
- Delete memory dump files- when critical errors occur, Windows stops its work and shows a BSOD (blue screen of death), at the same time saving information about running programs and drivers to a file for later analysis by special programs to identify the culprit of the failure. The option is almost useless, as it allows you to win only ten megabytes of free space. Clearing the memory dump files does not harm the system.
- Clear Recent Documents List- oddly enough, the option clears the Recent Documents list. This list is in the Start menu. You can also clear the list manually by right-clicking on this item in the Start menu and selecting "Clear Recent Items List". Useful option: I noticed that clearing the list of recent documents allows the Start menu to display its menus a little faster. The system will not be damaged.
- Clearing the TEMP Folder- The holy grail for those who are looking for the cause of the disappearance of free space on the C: drive. The fact is that in the TEMP folder, many programs store files for temporary use, forgetting to “clean up after themselves” later. A typical example is archivers. Unpack the files there and forget to delete. Clearing the TEMP folder does not harm the system, it can free up a lot of space (in especially neglected cases, the gain in free space reaches fifty gigabytes!).
- Adobe Flash Player - cleaning up temporary files- "flash player" can save files for temporary use. They can be removed. Sometimes (rarely) the option helps in combating Flash Player glitches. For example, with video and audio playback problems on the Vkontakte website. There is no harm in using.
- Clearing the cache of the terminal client- as far as I know, this option clears the temporary files of the Windows component called "Remote Desktop Connection" (remote access to computers via RDP protocol). Option seems to be does no harm, it frees up space from a dozen megabytes at best. There is no point in using it.
- IIS - Delete HTTP Error Log- long to explain what it is. Let me just say that it is better not to enable the option to clear the IIS log. In any case, it does no harm, no benefit either.
- Macromedia Flash Player- item duplicates "Adobe Flash Player - Cleaning Temporary Files", but affects rather ancient versions of the Flash Player.
- Java - cache clearing- gives a gain of a couple of megabytes on the hard drive. I do not use Java programs, so I did not check the consequences of enabling the option. I don't recommend turning it on.
- Emptying the trash- the purpose of this item is absolutely clear from its title.
- Delete system update installation logs- Windows keeps a log of installed updates. Enabling this option clears the log. The option is useless because there is no free space to win.
- Remove Windows Update protocol- similar to the previous paragraph, but other files are deleted. It's also a useless option.
- Clear the MountPoints database- if icons with them are not created in the Computer window when connecting a flash drive or hard drive, this option can help. I advise you to turn it on only if you have problems connecting flash drives and disks.
- Internet Explorer - clear cache- clears temporary files of Internet Explorer. The option is safe and useful.
- Microsoft Office - clear cache- cleans temporary files of Microsoft Office programs - Word, Excel, PowerPoint and others. I can't check the security options because I don't have Microsoft Office.
- Clearing the Cache of the CD Burning System- a useful option that allows you to delete files that you have prepared for burning to discs.
- Cleaning up the TEMP system folder- unlike the user's TEMP folder (see point 5), clearing this folder is not always safe, and it usually frees up a little space. I don't recommend turning it on.
- MSI - cleaning the Config.Msi folder- this folder contains various files created by program installers. The folder is large if the installers didn't complete their work correctly, so clearing the Config.Msi folder is justified. However, be warned - there may be problems uninstalling programs that use .msi installers (for example, Microsoft Office).
- Clear task scheduler logs- The Windows Task Scheduler keeps a log where it records information about completed tasks. I do not recommend enabling this item, because there is no benefit, but it will add problems - the Windows Task Scheduler is a rather buggy component.
- Delete Windows setup protocols- winning a place is insignificant, it makes no sense to delete.
- Windows - clear icon cache- useful if you have problems with shortcuts. For example, when the Desktop appears, the icons do not appear immediately. Enabling this option will not affect system stability.
- Google Chrome - clear cache is a very useful option. Google Chrome stores copies of pages in a folder designated for this purpose in order to open sites faster (pages are loaded from the hard drive instead of downloading via the Internet). Sometimes the size of this folder reaches half a gigabyte. Cleaning is useful in terms of freeing up hard drive space; neither Windows nor Google Chrome affects stability.
- Mozilla Firefox - Cleaning up the CrashReports folder- every time a problem occurs with the Firefox browser and it crashes, report files are generated. This option deletes the report files. The gain of free space reaches a couple of dozen megabytes, that is, there is little sense from the option, but there is. The stability of Windows and Mozilla Firefox is not affected.
Depending on the installed programs, the number of points will differ. For example, if the Opera browser is installed, you can clear its cache too.
Cleaning the list of startup programs
A sure way to speed up the computer's startup and speed is to clean the autorun list. If unnecessary programs do not start, then the computer will not only turn on faster, but also work faster too - due to the freed up resources that will not be taken away by programs running in the background.
AVZ is able to view almost all loopholes in Windows through which programs are launched. You can view the autorun list in the Tools - Autorun Manager menu:

An ordinary user has absolutely no use for such powerful functionality, so I urge don't turn everything off. It is enough to look at only two points - Autorun folders and run*.
AVZ displays autostart not only for your user, but also for all other profiles:

In chapter run* it is better not to disable programs located in the section HKEY_USERS- this may disrupt other user profiles and the operating system itself. In chapter Autorun folders you can turn off everything you don't need.
Lines marked in green are recognized by the antivirus as known. This includes both Windows system programs and digitally signed third-party programs.
All other programs are marked in black. This does not mean that such programs are viruses or anything similar, just that not all programs are digitally signed.
Don't forget to stretch the first column wider so you can see the name of the program. The usual unchecking will temporarily disable the autorun of the program (you can then tick it again), selecting the item and pressing the button with a black cross will delete the entry forever (or until the program writes itself back to autorun).
The question arises: how to determine what can be disabled and what is not? There are two solutions:
First, there is common sense: by the name of the .exe file of the program, you can make a decision. For example, Skype creates an entry during installation to automatically start when you turn on your computer. If you do not need it, uncheck the box ending with skype.exe. By the way, many programs (including Skype) can remove themselves from startup by themselves, just uncheck the corresponding item in the settings of the program itself.
Secondly, you can search the Internet for information about the program. Based on the information received, it remains to decide whether to remove it from autorun or not. AVZ makes it easy to find information about points: just right-click on the item and select your favorite search engine:

By disabling unnecessary programs, you will noticeably speed up the startup of your computer. However, it is undesirable to disable everything in a row - this is fraught with the fact that you will lose the layout indicator, disable the antivirus, etc.
Disable only those programs that you know for sure - you don't need them in autorun.
Outcome
In principle, what I wrote about in the article is akin to hammering nails with a microscope - the AVZ program is suitable for optimizing Windows, but in general it is a complex and powerful tool suitable for performing a variety of tasks. However, in order to use AVZ to its fullest, you need to thoroughly know Windows, so you can start small - namely, with what I described above.
If you have any questions or comments - under the articles there is a comment block where you can write to me. I follow the comments and will try to answer you as soon as possible.
Related posts:
Like
Like
dedicated AVZ, I want to share with you some more knowledge on the capabilities of this wonderful utility.
Today we will talk about system recovery tools, which can often save your computer's life after being infected with viruses and other horrors of life, as well as solve a number of system problems that arise as a result of certain errors.
It will be useful for everyone.
introductory
Before proceeding, traditionally, I want to offer you two formats of material, namely: video format or text. Video here:
Well, the text is below. See for yourself which option is closer to you.
General description of the program functionality
What are these recovery tools? This is a set of microprograms and scripts that help restore certain system functions to working condition. Which for example? Well, let's say, return or the registry editor, clear the hosts file or reset IE settings. In general, I give in full and with a description (so as not to reinvent the wheel):
- 1. Restore launch options.exe, .com, .pif files
This firmware restores the system's response to exe, com, pif, scr files.
Indications for use: after the removal of the virus, programs stop running. - 2. Reset Internet Explorer protocol prefix settings to default
This firmware restores protocol prefix settings in Internet Explorer
Indications for use: when you enter an address like www.yandex.ru, it is replaced by something like www.seque.com/abcd.php?url=www.yandex.ru - 3. Restoring the Internet Explorer start page
This firmware restores the start page in Internet Explorer
Indications for use: replacement of the start page - 4. Reset Internet Explorer search settings to default
This firmware restores search settings in Internet Explorer
Indications for use: When you click the "Search" button in IE, an external site is accessed - 5. Restore desktop settings
This firmware restores desktop settings. Restoration involves deleting all active ActiveDesctop elements, wallpapers, removing locks on the menu responsible for desktop settings.
Indications for use: The desktop settings tabs in the "Display Properties" window have disappeared, extraneous inscriptions or drawings are displayed on the desktop - 6. Remove all Policies (restrictions) current user.
Windows provides a user action restriction mechanism called Policies. This technology is used by many malware because the settings are stored in the registry and are easy to create or modify.
Indications for use: The functions of the explorer or other functions of the system are blocked. - 7. Deleting the message displayed during WinLogon
Windows NT and subsequent systems in the NT line (2000, XP) allow you to set the message displayed during startup. This is used by a number of malicious programs, and the destruction of the malicious program does not lead to the destruction of this message.
Indications for use: An extraneous message is introduced during system boot. - 8. Restoring File Explorer Settings
This firmware resets a number of File Explorer settings to default settings (the settings changed by malware are the first to be reset).
Indications for use: Changed explorer settings - 9. Removing system process debuggers
Registering a system process debugger will allow the application to be launched invisibly, which is used by a number of malicious programs.
Indications for use: AVZ detects unrecognized system process debuggers, problems with launching system components, in particular, the desktop disappears after a reboot. - 10. Restoring Boot Settings to SafeMode
Some malware, such as the Bagle worm, corrupts the system boot settings in Protected Mode. This firmware restores boot settings in protected mode.
Indications for use: The computer does not boot in safe mode (SafeMode). Use this firmware only if you have problems booting in protected mode. - 11. Unlock Task Manager
Task Manager blocking is used by malware to protect processes from detection and removal. Accordingly, the execution of this microprogram removes the lock.
Indications for use: Blocking the task manager, when you try to call the task manager, the message "Task manager has been blocked by the administrator" is displayed. - 12. Clearing HijackThis Ignore List
The HijackThis utility stores a number of its settings in the registry, in particular, a list of exclusions. Therefore, in order to disguise itself from HijackThis, the malware only needs to register its executable files in the exclusion list. A number of malicious programs are currently known to exploit this vulnerability. AVZ Firmware cleans up HijackThis utility exclusion list
Indications for use: Suspicions that the HijackThis utility does not display all information about the system. - 13. Cleaning up the Hosts file
Cleaning the Hosts file comes down to finding the Hosts file, removing all significant lines from it, and adding the standard string "127.0.0.1 localhost".
Indications for use: Suspicions that the Hosts file has been modified by a malicious program. Typical symptoms are blocking anti-virus software updates. You can control the contents of the Hosts file using the Hosts file manager built into AVZ. - 14. Automatic correction of SPl/LSP settings
Performs analysis of SPI settings and, if errors are found, automatically corrects the errors found. This firmware can be re-run an unlimited number of times. It is recommended that you restart your computer after running this firmware. Note! This firmware cannot be run from a terminal session
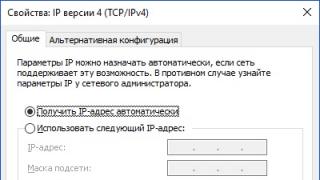
Indications for use: After removing the malicious program, access to the Internet was lost. - 15. Reset SPI/LSP and TCP/IP settings (XP+)
This firmware only works on XP, Windows 2003 and Vista. Its principle of operation is based on resetting and recreating SPI/LSP and TCP/IP settings using the standard netsh utility included with Windows. Details about resetting settings can be found in the Microsoft Knowledge Base - Please note! You should only use a factory reset if necessary if you have unrecoverable problems with Internet access after removing malware!
Indications for use: After removing the malicious program, access to the Internet was lost and the execution of the firmware "14. Automatic correction of SPl / LSP settings" does not work. - 16. Restoring the Explorer launch key
Restores the system registry keys responsible for launching File Explorer.
Indications for use: During system boot, explorer does not start, but manual launch of explorer.exe is possible. - 17. Unlock Registry Editor
Unlocks Registry Editor by removing the policy that prevents it from running.
Indications for use: It is impossible to start the registry editor, when you try, a message is displayed stating that its launch was blocked by the administrator. - 18. Full re-creation of SPI settings
Performs backup of SPI/LSP settings, then destroys them and creates according to the standard stored in the database.
Indications for use: Severe damage to SPI settings, unrepairable by scripts 14 and 15. Use only if necessary! - 19. Clear base MountPoints
Cleans up the MountPoints and MountPoints2 database in the registry.
Indications for use: This operation often helps in the case when, after infection with a Flash virus, disks cannot be opened in Explorer - On a note:
Restoration is useless if a Trojan program is running on the system that performs such reconfigurations - you must first remove the malicious program, and then restore the system settings
On a note:
To eliminate the traces of most Hijackers, you need to run three firmware - "Reset Internet Explorer search settings to default", "Restore Internet Explorer start page", "Reset Internet Explorer protocol prefix settings to default"
On a note:
Any of the firmware can be run several times in a row without damage to the system. The exceptions are "5. Restore Desktop Settings" (working with this firmware will reset all desktop settings and you will have to reselect desktop coloring and wallpaper) and "10. Restore Boot Settings in SafeMode" (this firmware recreates the registry keys responsible for booting in safe mode).
Helpful, isn't it?
Now about how to use.
Download launch, use
Actually everything is simple.
- Downloading from here(or from somewhere else) an anti-virus utility AVZ.
- Unpack the archive with it somewhere convenient for you
- We follow the folder where we unpacked the program and run it there avz.exe.
- In the program window, select "File" - "System Restore".
- Check the checkboxes for the items you want and click on the button. Perform marked operations".
- We are waiting and enjoying the result.
Here are the things.
Afterword
I must say that it works with a bang and eliminates a number of unnecessary gestures. So to speak, everything is at hand, quickly, simply and efficiently.
Thank you for your attention;)
I thank the masters of the Zapuskay.RF computer service center for their help in preparing the material. You can order repair of laptops and netbooks in Moscow from these guys.
Malicious programs that are introduced into the operating system of a personal computer cause significant harm to the entire amount of data. At this point in time, pest programs are created for different purposes, so their actions are aimed at correcting various structures of the operating system of a personal computer.
Common and obvious consequences to the user are problems with the Internet, disruptions in the operation of devices connected to the PC.
Even if the pest was detected and destroyed, this does not exclude the loss of information and other problems that arise in subsequent work. You can list the options endlessly, most often the user finds a complete or partial blocking of access to the World Wide Web, failure of external devices (mouse, flash card), an empty desktop, and so on.
The listed consequences are observed due to the changes that the pest program has made to the system files of a personal computer. Such changes are not eliminated with the elimination of the virus, they must be corrected independently, or resort to the help of specialists. In fact, this kind of work does not require special training, and any advanced user can perform it by studying the appropriate instructions.
In the practice of organizing the recovery of the operating system, there are several approaches, depending on the reasons that led to the failure. Let's consider each of the options in detail. An easy way available to every user is to roll back the OS to a restore point when the operation of the personal computer met the user's requirements. But very often this solution is unsatisfactory, or it is impossible to implement it for objective reasons.
How to restore the OS if the PC login is not possible?
Starting System Restore is as follows. Start Menu \ Control Panel \ System Restore. At this address, select the recovery point we need and start the process. After a while, the work will be completed and the computer is ready for normal operation. The technique is quite applicable to eliminate certain types of viruses, since changes also occur at the registry level. This option for restoring the operating system is considered the simplest and is included in the set of standard Windows tools. Step-by-step instructions and help with detailed comments on the process will help you master the method of restoring the health of your computer, even if the user does not feel completely confident as a PC administrator.
Another common OS recovery option is to run the procedure from external media. This option is complicated by some points, for example, you need to have a system image on a flash card or disk and take care of having such a copy in advance. In addition, it is often necessary to have certain skills in working with the BIOS system. An image of the operating system on external media is the best option if recovery is not possible because a virus has blocked the computer from entering the system. There are other options.
It is impossible to use the standard Windows tools to restore the OS if, for example, login is not possible, or there are other reasons that prevent the operation from being performed in standard mode. The situation is resolved using the ERD Commander (ERDC) tool.
How the program functions, we will analyze the situation sequentially. The first step is to download the program. The second step is to launch the Syst em Restore Wizard tool, it is with its help that the OS is rolled back to the specified recovery position.
As a rule, each tool has several checkpoints in stock, and in eighty percent of cases, the performance of a personal computer will be completely revived.
Using AVZ Utility Tools
The tool considered below does not require any special skills and abilities of the user. The software product was developed by Oleg Zaitsev and is designed to search for and destroy all types of viruses and malware. But in addition to the main function, the utility restores most of the system settings that have been attacked or changed by malware viruses.
What problems can the presented program solve? The main thing is the restoration of system files and settings that have been attacked by viruses. The utility copes with damaged program drivers that refuse to start after recovery. When there are problems working in browsers or in case of blocking access to the Internet and many other troubles.
We activate the restore operation at File \ System Restore and select the operation that is needed. The figure shows the interface of microprograms that the utility operates with, we will give a description of each of them.

As you can see, the set of operations is represented by 21 items, and the name of each of them explains its purpose. Note that the capabilities of the program are quite diverse and it can be considered a universal tool in the resuscitation of not only the system itself, but also the elimination of the consequences of viruses working with system data.
The first parameter is used if the consequences of a virus attack and the OS recovery procedures refuse to work the programs necessary for the user. As a rule, this happens if the pest has penetrated the files and program drivers and made any changes to the information recorded there.
The second parameter is necessary when the viruses performed the substitution of domains when entering them into the browser's search engine. Such a substitution is the first level of adjustment of the interaction between the system files of the operating system and the Internet. Such a function of the program, as a rule, eliminates the changes made without a trace, without trying to detect them, but simply by completely formatting the entire amount of prefix and protocol data, replacing them with standard settings.
The third parameter resumes setting up the Internet browser's start page. As in the previous case, by default, the program corrects the problems of the Internet Explorer browser.
The fourth parameter adjusts the work of the search engine and sets the standard mode of operation. Again, the procedure concerns the browser installed by Windows by default.
In case of a problem related to the functioning of the desktop (the appearance of banners, pictures, extraneous entries on it), the fifth item of the program is activated. Such consequences of the action of malicious programs were very popular a couple of years ago and caused a lot of problems for users, but even now such dirty tricks can penetrate the PC operating system.
The sixth point is necessary if the malware has restricted the user's actions when executing a number of commands. These restrictions can be of a different nature, and since access settings are stored in the registry, malicious programs most often use this information to adjust the user's work with their PC.
If a third-party message appears when the OS boots, it means that a malicious program has been able to infiltrate the Windows NT startup options. An OS restore that killed the virus does not remove this message. In order to remove it, you must activate the seventh parameter of the AVZ utility menu.
The eighth menu option, as the name suggests, restores Explorer settings.
Sometimes the problem manifests itself in the form of interruptions in the operation of system components, for example, during the startup of the PC OS, the desktop disappears. The AVZ utility diagnoses these structures and makes the necessary adjustments using item nine of the tools menu.
Problems booting the OS in safe mode are resolved by point ten. It is easy to detect the need to activate this item of the multiprogram of the utility considered here. They are shown at any attempts to carry out work in a security mode.
If the task manager is blocked, then menu item eleven must be activated. Viruses on behalf of the administrator make changes to the activation of this section of the operating system, and instead of the working window, a message appears stating that work with the task manager is blocked.
The HijackThis utility, as one of its main functions, uses the storage of a list of exclusions in the registry. For a virus, it is enough to penetrate the utility's database and register files in the registry list. After that, it can self-repair an unlimited number of times. The utility's registry is cleaned by activating the twelfth item of the AVZ settings menu.
The next, thirteenth point, allows you to clear the Hosts file, this file modified by a virus can cause difficulties when working with the network, block some resources, and interfere with updating the databases of anti-virus programs. Working with this file will be discussed in more detail below. Unfortunately, almost all virus programs seek to edit this file, which is due, firstly, to the simplicity of making such changes, and the consequences can be more than significant, and after the removal of viruses, the information entered in the file can be a direct gateway to penetration into OS new pests and spies.
If access to the Internet is blocked, then this, as a rule, means there are errors in the SPI settings. Their correction will occur if you activate the menu item fourteen. It is important that this setting item cannot be used from the terminal session.
Similar functions are included in the fifteenth menu item, but its activation is possible only with work in such operating systems as XP, Windows 2003, Vista. You can use this multiprogram if attempts to correct the situation with entering the network using the previous setting did not bring the desired result.
The possibilities of the sixteenth menu item are aimed at restoring the system registry keys that are responsible for launching the Internet browser.
The next step in the work of restoring OS settings after a virus attack is to unlock the registry editor. As a rule, an external manifestation - it is impossible to download a program for working with the Network.
The following four points are recommended only if the damage to the operating system is so catastrophic that, by and large, it makes no difference whether they are eliminated using such methods or, as a result, you need to reinstall the entire system.
So, the eighteenth paragraph recreates the original SPI settings. The nineteenth item clears the Mount Points /2 registry.
The twentieth item removes all static routes. Finally, the last, twenty-first item erases all DNS connections.
As you can see, the presented capabilities of the utility cover almost all areas into which a malicious program can penetrate and leave its active trail, which is not so easy to detect.
Since anti-virus applications do not guarantee 100% protection of your PC's operating system, we recommend that you have such a program in your arsenal of tools to combat computer viruses of all kinds and forms.
As a result of the treatment of the PC OS, the devices connected to it do not work.
One popular way to disguise spyware is to install your own virus driver in addition to the real software. In this situation, the actual driver is most often the mouse or keyboard file. Accordingly, after the virus is destroyed, its trace remains in the registry, for this reason the device to which the pest was able to join stops working.
A similar situation is observed with incorrect work in the process of removing Kaspersky Anti-Virus. This is also related to the specifics of the installation of the program, when its installation on a PC uses the auxiliary klmouflt driver. In the situation with Kaspersky, this driver must be found and completely removed from the personal computer system in accordance with all the rules.
If the keyboard and mouse refuse to function in the desired mode, the first step is to restore the registry keys.
Keyboard :
HKEY_LOCAL_MACHI NE\SYSTEM\Curren tControlSet\Control\Class\(4D36E 96B-E325-11CE-BF C1-08002BE10318)
UpperFilters=kbd classMouse :
HKEY_LOCAL_MACHI NE\SYSTEM\Curren tControlSet\Control\Class\(4D36E 96F-E325-11CE-BF C1-08002BE10318)
UpperFilters=mou class
The problem of inaccessible sites
The consequences of a malware attack may be the unavailability of certain resources on the Internet. And these consequences are the result of changes that viruses managed to make to the system. The problem is detected immediately or after some time, but if, as a result of the actions of pest programs, it manifested itself after some time, it will not be difficult to eliminate it.
There are two options for blocking, and the most common is updating the hosts file. The second option is to create fake static routes. Even if the virus is killed, the changes it made to these tools will not be removed.
The document in question is located in the system folder on drive C. Its address and location can be found here: C:\Windows\System 32\drivers\etc\hosts . For a quick search, as a rule, use the command line from the Start menu.
If the file cannot be found using the specified procedure, this may mean that:
— a virus program has changed its location in the registry;
- the file document has the "hidden" parameter.
In the latter case, we change the characteristics of the search. At the address: Folder Options / View we find the line "Show hidden files" and set the label opposite, expanding the search range.
The hosts file contains information about converting the literal name of the site's domain into its IP address, so malware programs write adjustments in it that can redirect the user to other resources. If this happens, then when you enter the address of the desired site, a completely different one opens. In order to return these changes to their original state and fix them, you need to find this file and analyze its contents. Even an inexperienced user will be able to see what exactly corrected the virus, but if this causes certain difficulties, you can restore the default settings, thereby eliminating all changes made to the file.
As for correcting routes, the principle of action is the same. However, in the process of interaction between the PC operating system and the Internet, the priority always remains with the hosts file, so restoring it is enough for work to be carried out in standard mode.
The difficulty arises if the desired file cannot be found, as the virus changes its location in the system folders. Then you need to fix the registry key.
HKEY_LOCAL_MACHI NE\SYSTEM\CurrentControlSet\serv ices\Tcpip\Parameters\DataBasePa th
Viruses belonging to the Win32/Vundo group are smarter than most of their malicious cousins when it comes to transforming hosts files. They change the file name itself, deleting the Latin letter o and replacing the sign with a Cyrillic letter. Such a file is no longer involved in converting domain names of sites into IP addresses, and even if the user restores this file, the result of the work will remain the same. How to find the real file? If there are doubts that the object we need is real, we perform the following procedure. The first step is to activate the display mode of hidden files. We examine the catalog, it looks like it is shown in the figure.

Here are two identical files, but since the OS does not allow the use of identical names, it is obvious that we are dealing with a false document. Determining which one is correct and which is not is easy. The virus creates a voluminous file with numerous adjustments, so the result of its wrecking in the figure is represented by a hidden file of 173 KB.
If you open a document file, the information in it will contain the following lines:
31.214.145.172 vk.com - a string that can replace the IP address of the site
127.0.0.1 avast.com is a file line written by a virus to prevent access to the site of the anti-virus program
We have already noted above that it is also possible to block individual resources by creating incorrect routes in the routing table. How to resolve the situation, consider the sequence of actions.
If the hosts file does not have malicious modifications, and it is impossible to work with the resource, the problem lies in the route table. A few words about the essence of the interaction of these tools. If the correct adaptive domain address is specified in the hosts file, then a redirect to this address to an existing resource occurs. As a rule, the IP address does not belong to the range of addresses of the local subnet, therefore, forwarding occurs through the gateway of the router, which is determined by the settings of the Internet connection.
If you adjust the route entries for a specific IP address, then the automatic connection will occur based on this entry. Provided there is no such route, or the gateway is down, the connection will fail and the resource will remain unavailable. Thus, a virus can delete an entry in the route table and block absolutely any site.
Routes created for specific sites remain in the HKLM registry database. Route updating occurs when the route add program command is activated or the data is manually corrected. When there are no static routes, the table section is empty. You can view a list of routing data by using the route print command. Will render it like this:

Active routes:

The above table is standard for a PC with a single network card and network connection settings:
IP address 192.168.0.0
mask 255.255.255.0
default gateway 192.168.0.1
The entry above includes the network IP address, coded 192.168.0.0, and the subnet mask, coded 255.255.255.0. If you decipher this data, then the information is as follows. The mask includes the entire scope of nodes with an equivalent high-order part of the address. According to the metric system, the first three bytes of the subnet mask are 1 in all PC operating systems (the exceptions are decimal, where the value is 255 and hexadecimal, where the value is 0*FF ). The low end of the received host address is a value in the range 1-254.
In accordance with the information presented above, the lowest address has an encoding - 192.168.0.0, this code is the network address. The high-order address, encoded 192.168.0.255, is characterized as a broadcast address. And if the first code excludes its use for data exchange, then the second code is just designed to perform these functions. Their nodes exchange data packets using routes.
Imagine the following configuration:
IP address - 192.168.0.0
Netmask - 255.255.255.0
Gateway - 192.168.0.3
Interface - 192.168.0.3
Metric - 1
The information is logically decoded as follows: in the address range from 192.168.0.0 - 192.168.0.255, we use the network card code (192.168.0.3) as a gateway and interface to exchange information. All this means that the information goes directly to the addressee.
When the end address condition does not match the given range 192.168.0.0-192. 168.0.255, it will not be possible to transfer information directly. The server protocol sends the data to the router, which forwards it to another network. If no static routes are specified, the default router address remains the same as the gateway address. Information is sent to this address, then to the network, and along the routes specified in the table, until the addressee receives the packet. In general terms, the data transfer process looks like this. Let's imagine an illustration of the entries in the standard router table. In the example, there are only a few entries, but their number can reach tens or hundreds of lines.
 Based on the example data, we will describe the process of redirecting to the addresses of an Internet resource in. During contact with Internet resource addresses located in the specified range from 74.55.40.0 to 74.55.40.255, the router code is equal to the network number 192.168.0.0, and therefore cannot be used in the process of exchanging information data. The IP protocol diagnoses an address (74.55.40.226) that is not included in the packet of addresses of an individual local network and refers to prescribed static routes.
Based on the example data, we will describe the process of redirecting to the addresses of an Internet resource in. During contact with Internet resource addresses located in the specified range from 74.55.40.0 to 74.55.40.255, the router code is equal to the network number 192.168.0.0, and therefore cannot be used in the process of exchanging information data. The IP protocol diagnoses an address (74.55.40.226) that is not included in the packet of addresses of an individual local network and refers to prescribed static routes.
The situation when this route is not specified, the information packet is sent to the gateway identification address set in the default example.
Since the route shown in the example has a high priority, it needs a specific gateway, not a standard that fits all. Since there is no gateway that satisfies the request in the table, the server with the network address 74.55.40.226 will remain out of range. And under the conditions prescribed in the example with the subnet mask code, all addresses in the range 74.55.40.0 - 74.55.40.255 will be blocked. It is this range that includes the network path to the site of anti-virus software installed on a personal computer, which will not receive the necessary virus database updates and will not function properly.
The more such data in the route table, the more resources are blocked. In the practice of specialists, virus programs created up to four hundred lines of this type, thereby blocking the work of about a thousand network resources. Moreover, the owners of viruses are not particularly interested in the fact that, in an effort to ban a particular resource, they exclude dozens of other sites from possible access. This is the main mistake of unscrupulous programmers, since the amount of inaccessible resources reveals the very possibility of blocking data transfer. So, for example, if the most popular social networks are included in the exclusion circle, and the user cannot enter the VKontakte or Odnoklassniki website, then a suspicion arises about the correct operation of the PC with the network.
Correcting the situation is not difficult; for this purpose, the route command and the delete key are used. We find false entries in the table and uninstall. A small note, all operations are feasible only if the user has administrator rights, but the virus can also make changes to the route only if it has infiltrated the network through the personal computer administrator account. We give examples of such tasks.
route delete 74.55.40.0 - an entry that deletes the first version of the route string;
route delete 74.55.74.0 - an entry that deletes the second version of the route string.
The number of such lines should be the total number of false routes.
If the approach to the procedure is simpler, then it is necessary to apply the operation of redirecting the output. This is done by entering the task route print > C:\routes.txt. Activating the command creates a situation where a file document called routes.txt is created on the system disk, it contains a table with route data.
The table list contains DOS character codes. These characters are unreadable and have no meaning for the operation. By adding a route delete task at the beginning of each route, we remove each false entry. These look like this:
route delete 84.50.0.0
route delete 84.52.233.0
route delete 84.53.70.0
route delete 84.53.201.0
route delete 84.54.46.0
Next, you need to change the file extension, the options for replacing such an extension are cmd or bat. A new file is launched by double-clicking the right mouse button. You can simplify the task with the help of the popular FAR file manager, which works as follows. The editor, which is called by the function key F 4, highlights the right part of the route entry with a special marking. Using the key combination CTRL + F 7, all spaces are automatically swapped to a character with an empty value, and the space, in turn, is set to the starting position of the line. The new combination of the specified keys sets the route delete task to the place we need.
When there are a lot of false routes in the data table and correcting them manually seems to be a long and tedious process, it is recommended to use the route task together with the F key.
This switch removes all non-nodal routes and also completely uninstalls routes with an endpoint and a broadcast address. The first and last have the digital code 255.255.255.255; the second 127.0.0.0. In other words, all false information written into the table by the virus will be uninstalled. But at the same time, the records of static routes written by the user themselves and the data of the main gateway will be destroyed, so they will need to be restored, since the network will remain inaccessible. Or monitor the process of cleaning the data table and stop it if you intend to delete the record we need.
The AVZ antivirus program can also be used to adjust the router settings. The specific multiprogram involved in this process is the twentieth item of the TCP configuration.
The last option for blocking user access to IP addresses of sites that are used by virus programs is to use DNS server address spoofing. In this case, the connection to the network occurs through a malicious server. But such situations are quite rare.
After the behavior of all work, it is necessary to reboot the personal computer.
Once again, I thank for the help in preparing the material the masters of the Zapuskay.RF computer service center - http://launch.rf/information/territory/Kolomenskaya/, from whom you can order laptop and netbook repairs in Moscow.